Understand what is penetration testing and why it is important to spend money to identify security vulnerabilities in your applications.
This cheatsheet is intended to run down the typical steps performed when conducting a web application penetration test. I will break these steps down into sub-tasks and describe the tools I recommend using at each level.

Make your applications attack-proof by penetration testing with Python. Learn how to customize and write your own tests with Python.
Penetration Testing Student (PTS) is tailored for beginners. This course starts from the very basics and covers Networking & Programming skills every Pentester should have.
Penetration testing (also called pen testing) is the practice of testing a computer system, network or Web application to find vulnerabilities that an attacker could exploit. Pen tests can be automated with software applications or they can be performed manually. Either way, the process includes
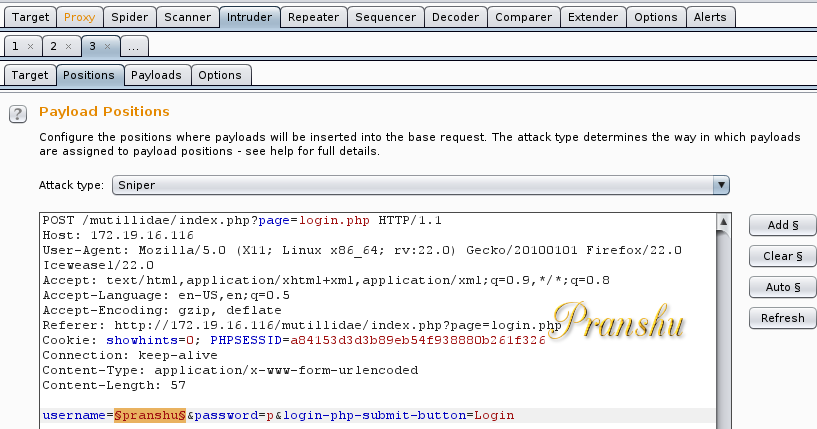
Burp Suite tutorial teaches you step-by-step how to easily configure your testing platform and execute thorough web application penetration tests using Burp

Protect your business from embarrassing security failures with Corsaire’s flagship penetration testing and information security consultancy services.
Pentest People offer penetration testing services with a fresh approach. We offer Internal and External assessments and access to …



Our Mobile and Web Application Penetration Testing Boot Camp focuses on preparing students for the real world of Mobile and Web Application Penetration Testing through lab exercises and lectures led by an expert instructor.


Learn web application penetration testing and ethical hacking through current course content, hands-on labs, and an immersive capture-the-flag challenge.

